Insights · Article · Security · Apr 2026
SPF, DKIM, alignment, gradual enforcement, and brand indicators that reduce phishing success without blocking legitimate marketing streams.

Modern phishing campaigns remain devastatingly effective because average users inherently trust familiar corporate brands displayed inside busy email inboxes. Attackers exploit this trust by impersonating known senders, embedding credential harvesting links behind logos that recipients recognize. The financial and reputational cost of a single successful brand impersonation attack can dwarf years of marketing investment, making email authentication not merely a security concern but a core business continuity requirement for every organization that relies on digital communication.
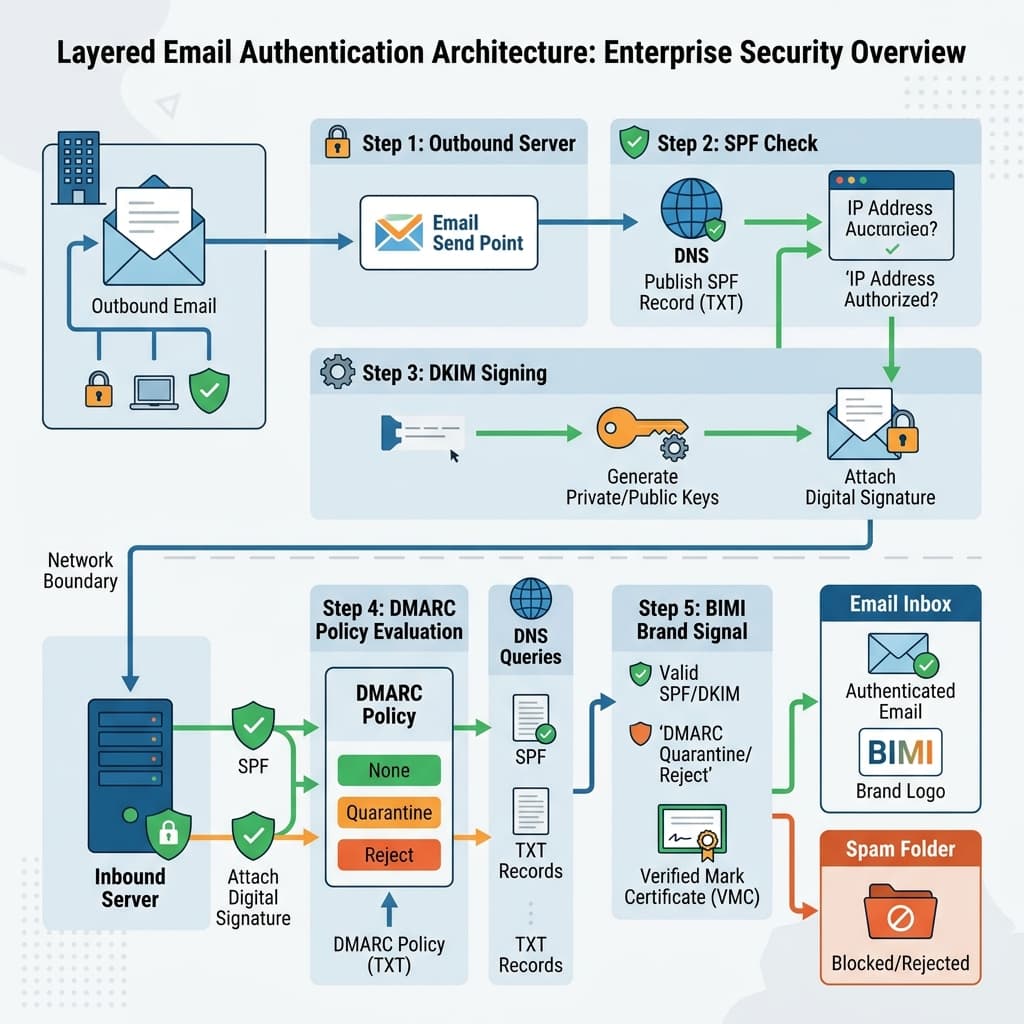
The Sender Policy Framework, commonly known as SPF, allows domain owners to publish a DNS record listing every IP address authorized to send mail on their behalf. When a receiving mail server encounters an inbound message, it checks the envelope sender domain against that published list. Messages originating from unlisted addresses fail the SPF check, giving the receiver a clear signal that the source may be fraudulent. SPF alone, however, cannot verify that the visible header from address matches the envelope sender, which creates a significant gap that attackers routinely exploit.
DomainKeys Identified Mail, or DKIM, closes part of that gap by attaching a cryptographic signature to each outbound message. The sending server signs specific header fields and the message body using a private key, then publishes the corresponding public key in DNS. Receiving servers validate the signature to confirm that nothing was altered in transit. DKIM proves message integrity and binds the content to a specific signing domain, but it still does not enforce a relationship between the signing domain and the address the end user actually sees.
Domain-based Message Authentication, Reporting, and Conformance ties SPF and DKIM together by introducing the concept of alignment. DMARC requires that either the SPF-authenticated domain or the DKIM signing domain matches the header from domain visible to the recipient. This alignment rule is what finally closes the impersonation loophole. DMARC also allows domain owners to publish an explicit policy telling receivers whether to quarantine or reject messages that fail alignment, transforming authentication from advisory guidance into enforceable instruction.
Authentication programs typically fail when internal marketing departments send campaigns through dozens of unverified domains without centralized inventory oversight. Before publishing any enforcement policy, security teams must compile a comprehensive, authoritative domain list that accounts for every subdomain, regional variation, and legacy alias. A thorough source IP and software vendor audit should follow, mapping each sending service to the domains it uses. Resolving subtle alignment mismatches at this stage prevents costly disruptions once stricter policies take effect.
We facilitate small-group sessions for customers and prospects without requiring a slide deck, focused on your stack, constraints, and the decisions you need to make next.
DMARC aggregate reports, delivered as XML files to addresses specified in your RUA tag, provide a daily summary of every authentication evaluation performed against your domain. These reports reveal which IP addresses are sending mail as your brand, whether those messages pass SPF and DKIM checks, and how receiving servers disposed of failures. Parsing these reports manually is impractical at scale, so most organizations feed them into a dedicated analytics platform that normalizes the data and highlights anomalies worth investigating.
Forensic reports, specified through the RUF tag, deliver individual message samples that failed authentication. While fewer mailbox providers generate these due to privacy concerns, the reports that do arrive offer invaluable detail for diagnosing specific alignment problems. Security teams must assign dedicated operational ownership to both report streams. Thousands of unread failure notifications sitting in a shared mailbox provide no actionable intelligence; they become noise that masks real threats hiding in plain sight.
Effective triage workflows route aggregate report anomalies into ticketing systems where analysts can classify unknown senders as either legitimate services needing authorization or hostile actors attempting impersonation. Establishing a regular cadence for reviewing report data, ideally weekly during the monitoring phase, ensures that new sending sources are identified and authorized before they trigger false positives. This discipline also builds the institutional knowledge required to confidently escalate enforcement without disrupting legitimate mail flows.
Successful gradual policy enforcement begins with a DMARC policy of none, which enables monitoring without affecting mail delivery. During this passive phase, the organization collects baseline data on all senders, resolves alignment gaps, and authorizes legitimate third-party services. Rushing past this stage is the single most common cause of self-inflicted email outages. Organizations should plan for a minimum monitoring period of four to six weeks, extending longer if the domain portfolio is large or the vendor ecosystem is complex.
The quarantine phase introduces incremental enforcement by telling receivers to route a percentage of failing messages to spam folders rather than the inbox. Starting at a low percentage, such as ten percent, and gradually increasing allows the security team to observe the impact on real mail flows in a controlled manner. If legitimate messages begin appearing in quarantine, the team can trace the alignment failure, update SPF records or DKIM signing configurations, and resume the ramp without widespread disruption to business communications.
Full rejection should only be applied after the quarantine percentage has reached one hundred percent and operated stably for several weeks with no legitimate mail being flagged. At this stage, the DMARC policy instructs receivers to outright reject messages that fail alignment, effectively preventing anyone without proper authorization from delivering mail under your domain. This is the posture that delivers the strongest brand protection, and it is also the prerequisite for enabling Brand Indicators for Message Identification.

Third-party sender integrations represent one of the most persistent sources of authentication failure. Marketing automation platforms, customer support tools, transactional email services, and HR notification systems all send mail on your behalf, often through infrastructure you do not control. Each vendor must be included in your SPF record or configured to sign messages with your DKIM key. Maintaining an up-to-date registry of authorized senders is essential, because vendors frequently rotate IP addresses and update their sending infrastructure without advance notice.
Contractual agreements with third-party senders should include explicit clauses mandating ongoing authentication maintenance, timely notification of infrastructure changes, and immediate breach disclosure whenever their systems send unauthorized messages bearing your domain. Service level agreements should specify maximum response times for resolving authentication failures. Without these contractual safeguards, your enforcement posture depends entirely on the operational discipline of external organizations whose priorities may not align with your security requirements.
Brand Indicators for Message Identification, or BIMI, layers a visual trust signal onto authenticated emails by displaying your brand logo directly in the recipient's inbox alongside the sender name. This logo appears only when all underlying authentication checks pass, effectively rewarding domain owners who have achieved full DMARC enforcement. For recipients, the logo provides an immediate visual cue that the message is genuinely from the claimed sender, reducing the likelihood that a spoofed message will earn their trust.
Implementing BIMI requires a Verified Mark Certificate issued by a qualified certificate authority, which validates that your organization legally owns the logo being displayed. The logo itself must conform to a strict SVG Tiny Portable Secure profile, a constrained vector format that prevents embedded scripts or external references. Internal legal and brand marketing teams should collaboratively own these logo assets alongside their renewal calendars, because an expired certificate or a malformed SVG file will silently remove your logo from every inbox that supports BIMI.
The user experience benefit of BIMI should not be underestimated. Research consistently shows that recipients engage more readily with branded messages, improving open rates and click-through performance for legitimate marketing campaigns. However, presenting a broken brand indicator path, where a logo intermittently appears and disappears due to certificate lapses or DNS misconfigurations, confuses end users far more than displaying no logo at all. Operational rigor around BIMI maintenance directly protects both brand perception and campaign effectiveness.
Human security awareness fundamentally complements this layered technology stack. Even the strongest authentication framework cannot prevent a well-crafted social engineering attack that arrives from a legitimately authenticated but compromised sender. Staff should be trained to verify contextual organizational details, such as unexpected requests for payment changes or credential resets, rather than relying solely on familiar brand icons. Phishing simulation exercises should be updated whenever your legitimate outbound mail patterns change, so that employees learn to recognize the difference between real and anomalous communications.
Measuring the effectiveness of your email authentication program requires tracking several complementary metrics. Aggregate phishing report volume should decline steadily as enforcement tightens. Credential stuffing attacks that correlate with brand impersonation campaigns offer a lagging indicator of reduced attacker success. Internal help desk tickets related to missing or delayed communications serve as an early warning system for legitimate mail being inadvertently blocked. Balancing cryptographic defense with reliable customer deliverability remains the central operational tension of any authentication deployment.
Corporate mergers, acquisitions, and divestitures introduce authentication risk at an accelerated pace. Newly acquired domains often carry legacy SPF records, orphaned DKIM keys, and no DMARC policy whatsoever. Inherited marketing automation platforms may send on behalf of the acquired brand through infrastructure that your security team has never reviewed. An enforced technical integration checklist, applied during due diligence and revisited at each integration milestone, prevents these newly joined domains from reintroducing the very impersonation vectors your authentication program was designed to eliminate.
Looking ahead, the email authentication landscape continues to evolve as major mailbox providers tighten inbound requirements. Google and Yahoo now mandate SPF, DKIM, and DMARC for bulk senders, and other providers are following suit. Organizations that treat authentication as a one-time project rather than an ongoing operational discipline will find themselves perpetually reacting to policy changes and deliverability crises. Building a sustainable program with clear ownership, automated monitoring, and contractual vendor accountability positions the brand for long-term resilience against both current and emerging impersonation threats.